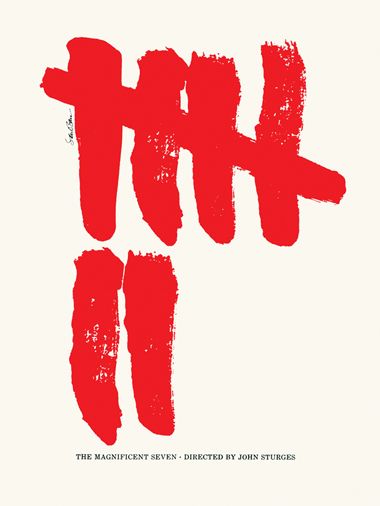
An implementation is like a movie, directed by leadership and produced by project management. Successful security implementation projects start strong, start with style, start like movies. As projects are running, what else can cinema teach us?
I began this series of cyber security design principles with an insight: to see things differently, look at different things. Spend a week with an artist, designer, or director. Find a security lesson. Share what I find. Sometimes my process is easy, sometimes difficult. Yet no one has challenged me more than Federico Fellini.
Federico Fellini. Distinctive, acclaimed, the Italian filmmaker was legendary in the twentieth century. He directed thirty-one films, “was nominated for twelve Academy Awards, and won four in the category of Best Foreign Language Film, the most for any director in the history of the Academy.” You’ve seen a movie scene inspired by (or directly copied from) a Fellini film. It’s guaranteed. Let’s take one example: Fellini’s Casanova. The film follows the titular Casanova on an adventure across Europe, while highlighting what makes Fellini a legendary director and a example for cyber security.
Anti-patterns in project management from Fellini’s Casanova:
- Micro-manage your people. “Puppets are happy to be puppets if the puppeteer is good,” Fellini said of his relationship with his actors. Donald Sutherland, who played Casanova, described it as being the worst experience of his filmmaking career. Every action micro-managed and scripted, until nothing of the talented actor remained.
- Force your people to fit your stereotype of talent. Sutherland is unrecognizable as Casanova. Fellini has him wearing a false chin and nose. He raised Sutherland’s hairline, which then necessitated false eyebrows to even the look out.
- Over-engineer details that don’t affect the final result. Fellini, unsatisfied with the color and waves from the water, had a plastic simulated lake created for Sutherland to row across. Almost a decade later, furious the color blue wasn’t the right color blue, Fellini would delay production while an entire faux ocean shore was created with plastic sheets for And the Ship Sails On.
James P. Carse popularized the idea of finite and infinite games. Most games we are familiar with are finite: you play to win, you play to maximize your results at the expense of the other players. Infinite games ongoing: you play to continue others to play. Federico Fellini films were finite games. Sutherland never worked with Fellini again. By contrast, the Golden Age of cinema was an infinite game. (Well, infinite, until it stopped in the 1950s.) Major film studios had in-house production crews and contracted actors. While the roles varied and films came and went, the directors were incentivized to keep the best people playing with them.
Cyber security in an organization is like the Golden Age of cinema. The leader’s role is encouraging people to want to play with us again and again, implementation after implementation.
Don’t be Fellini. Manage projects with the following patterns:
- Set the vision and collaborate with people on execution. Listen.
- Personalize the approach and tasks for the people on the project. Individualize.
- Maximize efforts where they matter by minimizing where they don’t. Simplify.
Directing implementation projects is both an art and a game. It is the art of engaging people in an infinite game. Good security projects leave people hungry to play again.
Afterwards
Security is often a story about crime, and criminals often make mistakes even while succeeding. Imagine someone stealing backup tapes to get at stored credit cards, not realizing they were also stealing people’s spreadsheets. In 1975, thieves broke into Technicolor labs and made off with film from 120 Days of Sodom. The heist also swooped up seventy reels of film from Casanova, forcing Fellini to reshoot weeks of material.
A good reminder to classify and protect data according to what criminals value … rather than what a snarky blogger might value.
This article is part of a series on designing cyber security capabilities. To see other articles in the series, including a full list of design principles, click here.