When work looks like work, work gets done. The concept is a cornerstone for my security philosophy. You want buy-in and adoption? Maximize specificity and familiarity.
But there’s a problem. The best way to keep things familiar is to keep things the same. Yet we design security capabilities to push things forward. When we push too far forward, when we push too hard, we lose people. Best case, we get low adoption. Worst case, we get outright revolt. So, on one end of the spectrum, we have comfortable stagnation. On the other end, uncomfortable transformation. How do we strike a balance?
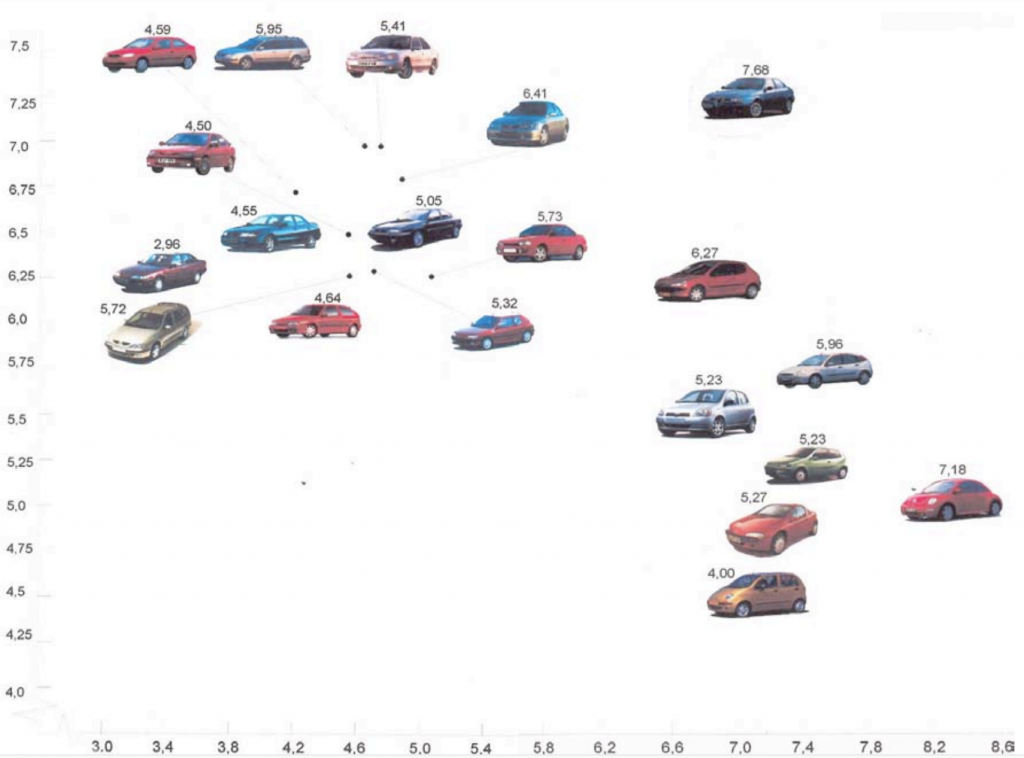
Paul Hekkert offers guidance. Hekkert has been working on the Unified Model of Aesthetics. The research starts with a very simple question: why do we like things? Hekkert’s team has found that it comes down to acting on similar but opposing ideas: unity versus variety, connectedness versus autonomy, typicality versus novelty. The last pair addresses our problem as security designers.
“People find those products the most beautiful that are the most sophisticated but at the same time comprehensible and familiar. That is the boundary that designers need to work with. It’s a fine line that varies between users,” Hekkert explained to TU Delft. “It does not mean that everyone has a different idea about what is beautiful. In very many respects, we agree on what is beautiful or new, particularly if we share a similar background, come from the same culture, or have had similar experiences. A principle such as this can help us understand why and when people find the same things beautiful or, in contrast, differ in taste.”
Balancing familiarity with novelty brings joy. Previously, we talked about leveraging the metaphor to bring understanding. In both cases, the underlying idea is calibrating the pace of change to the end-user’s sensibilities. For example, rolling out a new IAM/IGA tool for managers to review and certify access (Identity Access Management / Identity Governance and Administration). If people are already doing access reviews, the novelty of an easier user interface which is consistent with the metaphor of least privilege can bring a bit of joy. It’s easier. It’s faster. At a minimum, it’s an acceptable change.
Most Advanced, Yet Acceptable (MAYA) is the name Hekkert has given this principle. How advanced can the design be while still remaining familiar, still being acceptable, still looking like work? The answer will vary from organization to organization due to culture. But the question must remain top of mind for security leaders pushing the envelope.
This article is part of a series on designing cyber security capabilities. To see other articles in the series, including a full list of design principles, click here.
Posted by