Expos and tradeshows never end well. When the show’s over, many become ghost towns. Many more end up in the trash. Annually, the estimate is 600,000 tons of waste. So, it’s no surprise the recyclable People’s Pavilion at Dutch Design Week caught my attention.
The People’s Pavilion also gave me insights into a question people frequently ask: how can security programs get the most out of what they have? The answer is complicated because much of security comes from outside of the security program.
Take the CIS Critical Security Controls, for example. At the time of this article, the current version is 7.1 published last April 2019. As you read through the controls, it becomes obvious most are not owned by the security function. More than half the controls are well-configured IT. IT inventory and configuration, IT monitoring, IT backup and recovery. Add a well-configured perimeter, wired, and wireless network. In fact, it isn’t until the last few controls that security takes a front seat. Awareness training, incident response, and penetration testing. IT is the majority and the priority in the CSC.
In the beginning of my career, security was another word for doing IT right. Well-configured IT. This thinking may make a comeback as misconfigurations are rise as a cause of security breaches. In the Verizon Data Breach Investigations Report (DBIR), they write: “Errors definitely win the award for best supporting action this year. They are now equally as common as Social breaches and more common than Malware, and are truly ubiquitous across all industries. Since 2017, Misconfiguration errors have been increasing” and account for more than 40% of errors in the 2020 report.
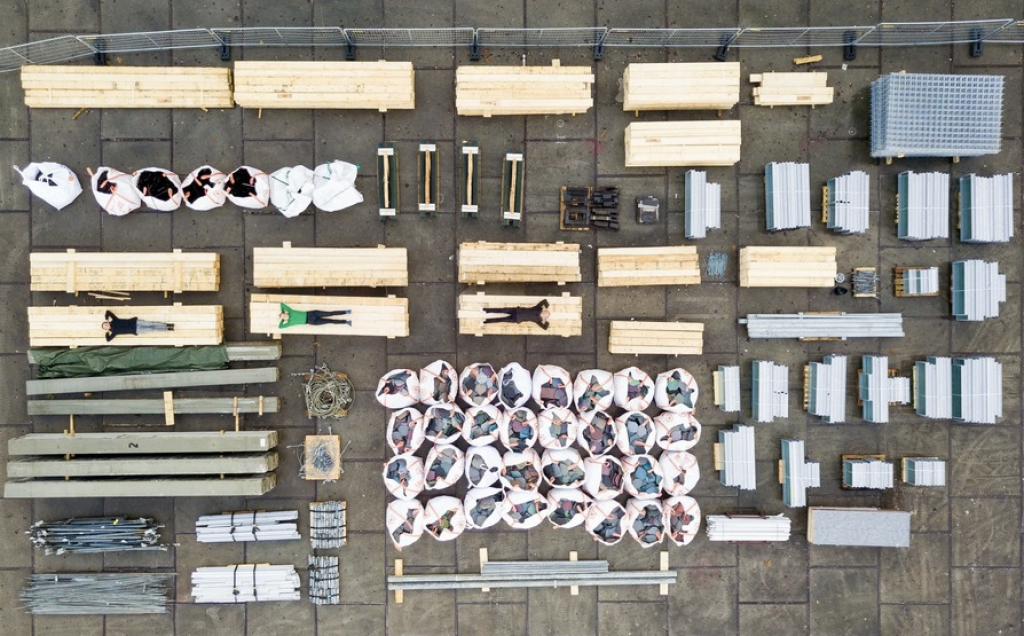
Back to the People’s Pavilion at Dutch Design Week 2017. “The building is a design of bureau SLA & Overtreders W. The designers have given a radical new impulse to the notion of a circular economy: the pavilion is made with 100% borrowed materials. Materials from suppliers and producers, but also from Eindhoven residents. Concrete and wooden beams, facade elements, glass roof, recycled plastic cladding: everything is borrowed for 9 days and will be returned to the owners after the DDW.” To demonstrate nothing went to waste, they photographed all the materials when received and when returned. The images were identical, documenting the full process.
When building and implementing a security capability, consider it like the People’s Pavilion, with a majority of the components coming from the IT team. Determine what those parts are. Determine how they’re supplied (with, for example, SIPOC diagrams.) Determine who will be responsible (with, for example, RASCI charts.) Reduce any waste in building the security capability. And finally, to prepare for future projects, design for disassembly.
To get the most out of a security program, begin with the configuration and operation of secured IT. Then reduce any wasted effort and smooth out the hand-off between security and IT.
This article is part of a series on designing cyber security capabilities. To see other articles in the series, including a full list of design principles, click here.
Posted by