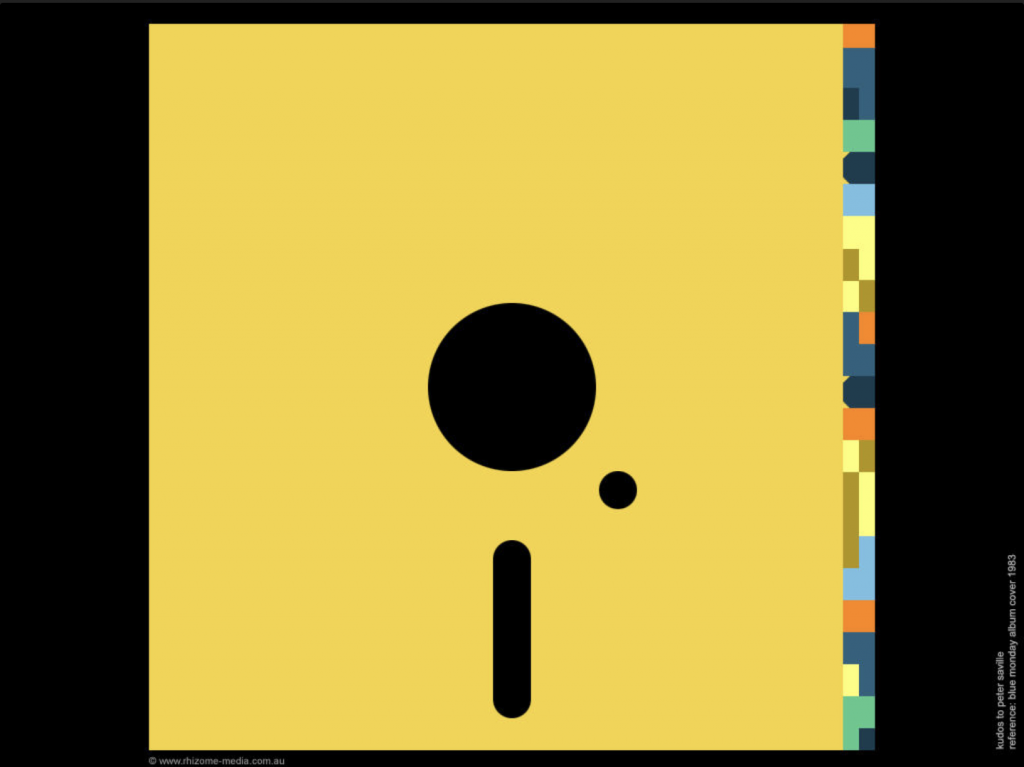
Peter Saville never listened to the music before designing the album cover. The Joy Division’s Unknown Pleasures cover with the pulsar. New Order’s Blue Monday and the iconic floppy disk cover. Saville designed without all the information and this always bothered me.
A pervasive thought in CyberSecurity is that people don’t implement controls because they’re not knowledgeable. More information means better security. The entire discipline of security awareness is based on this idea. But is this correct? Some studies suggest otherwise. Take User Mental Models of the Internet and Implications for Privacy and Security, for example. Researchers found that people with technical in-depth knowledge of the Internet didn’t actually take any more steps to protecting their information than non-technical people.
Our capacity is finite. We can hold three ideas in our mind. We can remember seven digits in a sequence. We can maintain a hundred-fifty relationships with people. Our semantic memory can only hold so many facts. The question is how we use that capacity. The goal is to fill our lives with right ideas, the right facts, the right people. In other words, the right amount to take action.
Back to Peter Saville. Saville knew art. He knew symbols, shape, and color. He didn’t know what a floppy disk was before hanging out with New Order’s band. He certainly did not know binary. (His code was a base-10 system.) He put it this way: “I understood the floppy disk contained coded information and I wanted to impart the title in a coded form, to simulate binary code in a way-therefore converted the alphabet into a code using colours.” The resulting cover was the striking floppy disk with the color-coded wheel. In the end, Saville knew exactly what he needed to know to do what he needed to do. Blue Monday became one of the most recognizable covers in the late twentieth century.
When designing the specific security controls, the trick is to be Peter Saville. On the one end of the spectrum are those who don’t understand the technology enough to take action. Picture the clueless boss stereotype. On the other end are those who understand it too much and get too deep into the implementation. Consider a firewall engineer who moved into security and now spends way too much time on network security, at the expense of the rest of the security program.
Determine how much information you need to take steps towards implementing security controls. The CyberSecurity architect sets the requirements. The IT subject matter expert implements technology to meet the requirement. Know enough, yes. But don’t waste time listening to the music.
This article is part of a series on designing cyber security capabilities. To see other articles in the series, including a full list of design principles, click here.
Posted by